Don’t spend more on coffee for your employees than you do on protecting your business from cyber threats.
Why Cybersecurity Matters More Than Ever
In today’s digital age, cyber threats are evolving at an unprecedented rate. Small and medium-sized businesses (SMBs) are no longer flying under the radar of cybercriminals. In fact, attackers now actively target SMBs because they know these organizations often have fewer defences in place compared to large enterprises. The reality is stark: 60% of SMBs close within six months of a cyberattack (source: U.S. National Cyber Security Alliance). Hackers don’t discriminate; they follow the path of least resistance. If your systems are exposed, your business is at risk.
Investing in affordable 24/7 enterprise-grade cybersecurity is no longer a “nice to have”—it’s mission-critical. While providing daily coffee might boost employee morale, ensuring their digital workspace is secure safeguards your company’s future. Threats are rising because business has changed. Work is remote and hybrid. Data sits across laptops, cloud apps, and mobile devices. A single stolen password can open email, files, and finance tools. AI now powers convincing phishing, and criminals automate scans for unpatched systems and misconfigured backups. They want quick payouts, not headlines.
Supply-chain risk compounds it. If a small vendor is compromised, an attacker can pivot into larger customers. Regulations and contracts now expect proof of controls. In Québec, Law 25 increases accountability and fines. Cyber insurers also demand basics like MFA (multi-factor authentication), EDR (endpoint detection and response), immutable backups, and 24/7 monitoring to keep coverage affordable. The business case is simple: continuous security reduces downtime, protects cash flow, and preserves client trust. It often lowers premiums and speeds vendor approvals—avoiding the hidden tax of breaches: lost sales, crisis PR, and emergency IT spend.
The Real Cost of Cybersecurity—It’s Less Than You Think

Many business owners hesitate to invest in cybersecurity, assuming that enterprise-grade solutions are prohibitively expensive. This misconception lingers from a time when only Fortune 500 companies could afford advanced security teams and technology.
Today, that’s changed. Advances in automation, artificial intelligence (AI), and managed security services have dramatically reduced costs. You don’t need an in-house Security Operations Centre (SOC) staffed with 20 analysts to achieve 24/7 protection. Instead, you can subscribe to a managed cybersecurity service for a fraction of the price—less than the cost of a daily cup of coffee per employee.
Here’s what that small daily investment buys you:
24/7/365 Monitoring & Threat Containment
Your IT infrastructure is monitored around the clock, every day of the year. Suspicious activity is flagged and addressed immediately. If an attacker tries to breach your defences at 2:00 a.m. on a Sunday, the system responds instantly—before the threat escalates.
Advanced Antivirus (AV)
Modern AV goes far beyond the basic protection you remember from the early 2000s. Today’s AV tools integrate machine learning to detect new, never-before-seen threats. They quarantine malicious files automatically and keep your employees’ devices safe from common malware, spyware, and trojans.
Endpoint Detection & Response (EDR)
Every device in your company—laptops, desktops, tablets, and even mobile phones—is a potential entry point for attackers. EDR continuously monitors these endpoints for unusual activity, such as unauthorized file transfers or login attempts. If something looks wrong, the system can isolate the device and stop the spread.
Ransomware Detection
Ransomware remains one of the most devastating forms of attack. Criminals encrypt your data and demand payment to restore access. With specialized ransomware detection, abnormal file encryption patterns are identified in real time, cutting off the attack before critical data is locked away.
DNS Protection Firewall
A DNS firewall acts like a security guard at the front door of your business. When an employee clicks a malicious link or accidentally visits a phishing website, the firewall blocks the request before it can connect. This reduces risk from human error, which remains the top cause of breaches.
Proactive Threat Hunting
Rather than waiting for alarms, cybersecurity experts actively hunt for indicators of compromise (IOCs). This proactive approach spots hidden intrusions—such as dormant malware or unauthorized accounts—before they activate.
Weekly Security Updates
Attackers exploit known vulnerabilities in software. That’s why keeping systems patched is critical. Weekly updates ensure your defences remain strong against the latest exploits.
The Hidden Expenses of Neglecting Cybersecurity

Some business leaders still view cybersecurity as a cost centre. The truth? Skimping on security can be far more expensive. Let’s break down the real risks.
Financial Losses
Cybercrime costs the global economy over CAD $10 trillion annually by 2025 (Cybersecurity Ventures). For SMBs, even a single incident can result in devastating losses: direct theft of funds, extortion payments, and weeks of lost revenue during downtime.
Reputation Damage
Customer trust is fragile. One breach can permanently damage your brand image, especially if sensitive client data is stolen. A lost reputation is often impossible to rebuild, especially in industries like healthcare, finance, and retail.
Legal Repercussions
Regulatory fines can be crippling. In Quebec, for example, Law 25 requires businesses to protect personal information. Failure to comply can result in fines of up to CAD $25 million or 4% of annual revenue—whichever is higher.
Operational Disruption
Cyberattacks grind operations to a halt. Ransomware can lock employees out of critical systems, while distributed denial-of-service (DDoS) attacks can take your website offline. Productivity plummets, clients are frustrated, and revenue disappears.
Investing Wisely for Peace of Mind
Cybersecurity is not just an expense—it’s a business enabler. By allocating a fraction of your budget to managed cybersecurity, you’re investing in:
- Data protection: Safeguarding customer and proprietary information.
- Customer trust: Demonstrating accountability and professionalism.
- Business continuity: Ensuring operations remain resilient, even under attack.
- Competitive advantage: Showing prospects that your business takes security seriously.
Think of it like insurance, but better. Instead of paying out after a disaster, cybersecurity prevents the disaster in the first place.
It also delivers measurable ROI: fewer outages, faster recovery times (RTO/RPO), and lower cyber-insurance premiums. Managed services convert unpredictable break/fix spend into a fixed monthly operating cost with defined SLAs. You gain expert monitoring, tested incident response, immutable backups, and quarterly tabletop exercises—capabilities most SMBs can’t staff in-house. Strong controls simplify audits (e.g., Law 25, PIPEDA), accelerate vendor onboarding, and protect cash flow during crises. Clear reporting—blocked threats, patch coverage, phishing risk—keeps boards informed and regulators satisfied. In short: invest a little each month to avoid six-figure emergencies and reputational damage later.
A Small Price for Significant Protection
Let’s return to the coffee analogy. An average cup of coffee in Canada costs around CAD $3. If you have 20 employees, that’s roughly CAD $60 per day, $300 per week, and over $15,000 per year. Stretch that across the full year—including holidays—and you’re funding a recurring expense that delivers a short morale boost but no risk reduction.
For less than this, you can protect your business with a fully managed, enterprise-grade security stack: monitoring, antivirus, EDR (endpoint detection and response), DNS protection, ransomware defence, and more. The spend becomes predictable OpEx with clear SLAs and monthly reporting. You also unlock bundled value—security awareness training, phishing simulations, and backup checks—without hiring extra staff.
Consider the alternative. If 10 employees sit idle for four hours due to a ransomware incident, and your blended cost is CAD $150/hour, that lost productivity alone is CAD $6,000—before recovery, reputational harm, or penalties. Redirect a modest slice of discretionary perks to continuous protection. It’s not a question of affordability—it’s a question of priorities, resilience, and keeping clients’ trust.
Why SMBs Are Attractive Targets
You might assume cybercriminals focus on large corporations with deeper pockets. While that’s partly true, SMBs are now their top targets. Here’s why:
- Faster payouts – Criminals assume SMBs will pay ransoms quickly to resume operations. Cash flow is tight. Downtime hurts. Attackers exploit that urgency with “discounted” ransom timers and double-extortion threats.
- Perceived as easier targets – Attackers know many SMBs lack full-time security staff. They expect weak basics: single-factor logins, stale patches, flat networks, and shared admin accounts. Automated scanners probe for these gaps 24/7.
- Supply chain leverage – Hacking an SMB often provides a backdoor into larger partners. A compromised vendor email account can push malicious invoices, change banking details, or deliver malware through trusted channels.
- Valuable data – Even small firms store sensitive customer information. Identity data, payment details, health records, and IP fetch high prices on criminal markets. Data theft now often precedes ransomware.
- Tooling asymmetry – Attackers reuse off-the-shelf kits, phishing frameworks, and AI-written lures. They scale cheaply. Defenders must cover many systems and users.
- Compliance pressure – Laws (e.g., Law 25, PIPEDA) and cyber-insurance questionnaires raise stakes. Gaps create legal, contractual, and premium risk—making SMBs tempting and profitable targets.
What Good Looks Like: An SMB Security Posture
When an SMB invests in enterprise-grade cybersecurity, here’s what the “before and after” picture looks like:
- Before: Infrequent software updates, free antivirus, no monitoring, no formal incident response plan.
- After: Weekly patching, AI-driven AV, EDR on every endpoint, 24/7 SOC monitoring, and tested incident response.
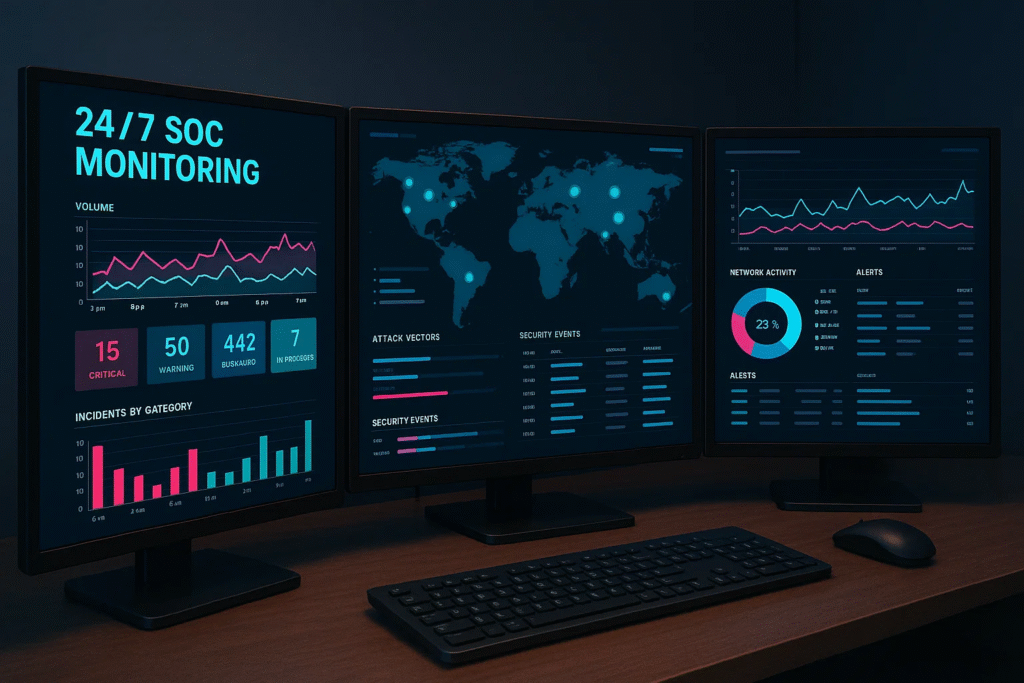
This transformation reduces the chance of a successful attack from “when, not if” to a far lower likelihood—while ensuring any incident is contained rapidly.
Add the essentials that separate “good” from “great”: enforce MFA (multi-factor authentication) everywhere, apply least-privilege access, and manage devices with MDM (mobile device management) for encryption and remote wipe.
Segment networks to prevent lateral movement and deploy email security with SPF, DKIM, and DMARC to stop spoofing. Maintain immutable, off-site backups with defined RPO/RTO targets and quarterly restore tests. Centralize logs in a SIEM with alerting and playbooks; measure MTTD/MTTR and tune monthly.
Run phishing simulations and short, quarterly training. Keep an asset inventory and a 30-/14-/7-day patching cadence based on risk. Formalize vendor risk reviews and name a privacy officer for Law 25/PIPEDA alignment. Finally, conduct tabletop exercises twice a year with IT, finance, and leadership so roles are clear, decisions are fast, and recovery is predictable.
Action Steps for Business Leaders
If you’re a business owner or decision-maker, here’s how to move forward:
- Assess your risk. Map critical systems, crown-jewel data, and third-party connections. Confirm who has admin rights, where backups live, and your current RTO/RPO targets.
- Talk to a provider. Choose a partner that offers 24/7 monitoring, EDR, and clear SLAs. Ask for sample reports, escalation paths, and breach communication templates.
- Prioritize quick wins. Turn on MFA everywhere, patch high-risk assets, and deploy DNS filtering. Enable device encryption and auto-isolation for suspicious endpoints.
- Train your people. Run monthly micro-lessons and phishing simulations. Track click rates and remediate with short coaching, not blame.
- Budget realistically. Treat protection as fixed OpEx. Bundle monitoring, backups, and response into one managed plan; align spend to risk reduction and insurance requirements.
- Validate. Test restores quarterly and run a 60-minute tabletop twice a year with IT, finance, and leadership. Measure MTTD/MTTR and improve.
The Future of SMB Cybersecurity
Cyber threats will only become more sophisticated with time. Artificial intelligence (AI) is already being used by attackers to automate phishing, craft deepfake voice notes, and probe for vulnerabilities at scale. Expect more identity attacks—session hijacking, MFA (multi-factor authentication) fatigue, and OAuth consent abuse—because identities now sit at the core of most breaches.
The good news: AI is also powering defence systems. Managed detection and response (MDR) platforms use behavioural analytics to flag anomalies within seconds and trigger automated containment. Security orchestration, automation, and response (SOAR) will take routine work off your team’s plate—resetting credentials, isolating hosts, and blocking malicious domains without waiting for human intervention. Passwordless authentication (passkeys) and stronger device trust will shrink the attack surface.
Network edges are dissolving. Remote and hybrid work make zero trust the default: verify explicitly, enforce least privilege, and continuously evaluate device health. Cloud misconfigurations remain a leading risk, so expect continuous posture management across Microsoft 365, Google Workspace, and SaaS apps, plus immutable, off-site backups by default. For connectivity, SASE (secure access service edge) and ZTNA (zero-trust network access) will replace legacy VPNs and flat networks.
Third-party and supply-chain risk will draw more scrutiny. Clients, regulators, and insurers will increasingly demand proof of cyber resilience before signing contracts or issuing coverage. In Québec and across Canada, Law 25 and PIPEDA expectations will push formal privacy roles, data mapping, and rapid breach reporting. Buyers will ask for SBOMs (software bills of materials), phishing-training metrics, and recovery times (RTO/RPO). SMBs that can show continuous controls monitoring—clear dashboards, tested restores, and fast MTTR—will win deals faster, secure better insurance terms, and operate with fewer costly surprises.
Take Action Today
Don’t let misconceptions about cost keep your business exposed. For less than the price of a daily coffee per employee, you can safeguard your company’s data, reputation, and future.
Cybersecurity is not just about protecting devices. It’s about protecting livelihoods, employees, customers, and the very survival of your business.
Take one practical step now: get a brief risk assessment and baseline controls in place—MFA, EDR, 24/7 monitoring, curated patching, and immutable backups. Confirm your recovery times (RTO/RPO), test a restore, and run a short tabletop exercise with IT, finance, and leadership. These actions cut the likelihood and impact of an incident, demonstrate diligence to clients and insurers, and support compliance (e.g., Law 25, PIPEDA). You’ll gain clear reporting—blocked threats, phishing results, patch coverage—so you can show stakeholders real progress, not promises.
Add cyber to the same category as payroll, insurance, and bookkeeping: non-negotiable. The next phishing email or credential-stuffing attempt won’t wait for budget season. A modest monthly subscription to managed security buys real outcomes—fewer outages, faster containment, cleaner audits, and better insurance terms. It also protects sales cycles; more RFPs now ask for evidence of controls, training, and tested backups. Show that you meet the mark and move deals forward. If you do nothing, you’re accepting avoidable downtime, emergency spend, and reputational risk. Choose predictable protection instead of unpredictable crises.
The cost of prevention is always less than the cost of a cure. Invest wisely, protect proactively, and ensure your business is fortified against today’s and tomorrow’s cyber threats.
Featured links:
National Cyber Security Alliance – SMB Resources
Government of Canada – Cyber Security for Small and Medium Businesses
Managed Cybersecurity Services
FAQ:
Why should SMBs invest in cybersecurity if they already use antivirus software?
Traditional antivirus is no longer enough. Cybercriminals exploit gaps like phishing, unpatched systems, and weak credentials. Enterprise-grade cybersecurity adds 24/7 monitoring, endpoint detection and response (EDR), ransomware defence, and proactive threat hunting—covering far more than antivirus alone.
Is enterprise-grade cybersecurity affordable for small businesses?
Yes. Thanks to automation and managed services, SMBs can now access 24/7 protection for less than the cost of a daily coffee per employee. It’s a predictable monthly investment that prevents unpredictable six-figure breach costs.
How does cybersecurity help with compliance in Québec and Canada?
Laws like Québec’s Law 25 and PIPEDA require businesses to safeguard personal data, report breaches, and designate accountability. Managed cybersecurity ensures these requirements are met, reducing risk of fines, lawsuits, and reputational damage.
What’s the most common way SMBs are breached?
Most incidents start with stolen passwords or phishing emails. Criminals also exploit unpatched systems and unsecured remote access. That’s why multi-factor authentication (MFA), DNS filtering, and regular patching are critical.
What’s the business benefit beyond protection?
Strong cybersecurity builds customer trust, helps secure contracts (especially with larger partners), lowers cyber-insurance premiums, and keeps operations running. It’s both a risk reducer and a growth enabler.
Problem
SMBs face constant, targeted cyber threats and often lack round-the-clock defences.
Impact
A single breach drives downtime, legal exposure (e.g., Law 25), reputational damage, and outsized financial loss.
Solution
Deploy 24/7/365 managed security—EDR (endpoint detection and response), ransomware detection, DNS filtering, proactive threat hunting, and weekly patching—for less than a daily coffee per employee.
Consequence
You cut breach likelihood, speed containment, protect revenue and trust, and keep operations running; neglect leaves you exposed to costly disruption and penalties.
Our Cybersecurity Guarantee
“At Fusion Cyber Group, we align our interests with yours.“
Unlike many providers who profit from lengthy, expensive breach clean-ups, our goal is simple: stop threats before they start and stand with you if one ever gets through.
That’s why we offer a cybersecurity guarantee: in the very unlikely event that a breach gets through our multi-layered, 24/7 monitored defenses, we will handle all:
threat containment,
incident response,
remediation,
eradication,
and business recovery—at no cost to you.
Ready to strengthen your cybersecurity defenses? Contact us today for your FREE network assessment and take the first step towards safeguarding your business from cyber threats!